Innovative Cyber Security & Compliance Services to
Build Cyber Resilience from Inside Out
Royal Cyber – Cyber Security & Compliance Services helps organizations protect, detect, react and recover across all touch points of IT security lifecycle

Comprehensive Cyber Security & Compliance Services
Our Cyber Security & Compliance Services Include:
Let’s Start a Conversation
Cyber Security and
Compliance Challenges
Royal Cyber Partnered With Leading IAM Vendors
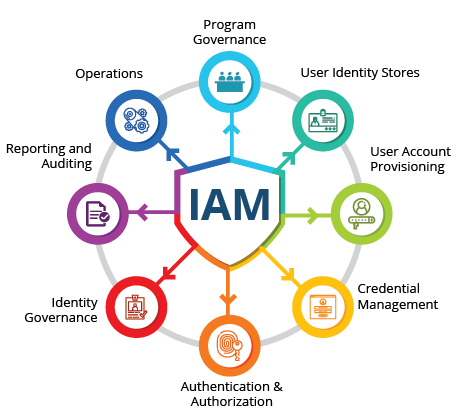
Identity
Governance
IBM Security Identity Governance & Intelligence (ISIGI/IGI)
Identity Management
(IAM)
Access Management
IBM Security Access Manager (ISAM)
Compliance
IBM Bigfix
Directory
Services
IBM Security Directory Server (ISDS)
Directory Integrator Services
IBM Security Directory Integrator (ISDI)
Get your Building Blocks Ready for Cyber Security & Compliance with Royal Cyber!
Royal Cyber Strategy
Royal Cyber strategy for Cyber Security & Compliance: